The Goal
To bridge the gap between a purely technical vulnerability scan and a business-level risk management decision. My objective was to simulate the entire lifecycle, from initial discovery using a scanner to creating an auditable remediation plan that a Governance, Risk, and Compliance (GRC) team could immediately use.
The Setup
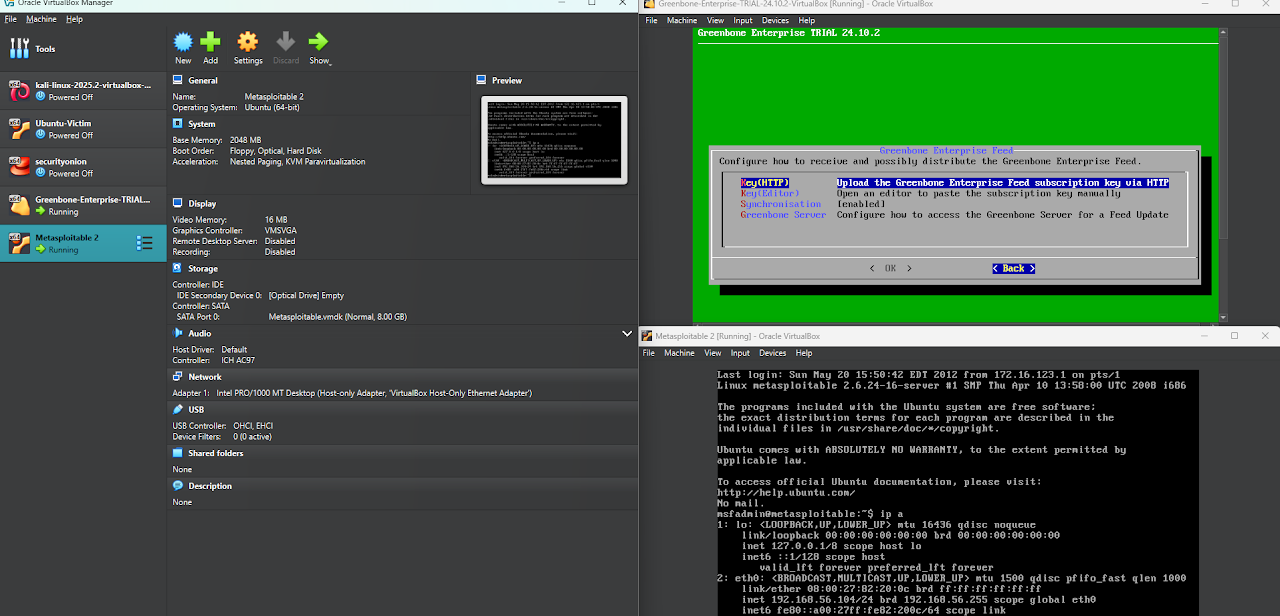
I constructed a secure, isolated lab environment in VirtualBox using a host-only network. The lab consisted of a Greenbone Community Edition (OpenVAS) virtual machine to act as the vulnerability scanner and a Metasploitable 2 VM, a Linux server intentionally configured with a wide range of common security flaws to serve as the assessment target.
The Process
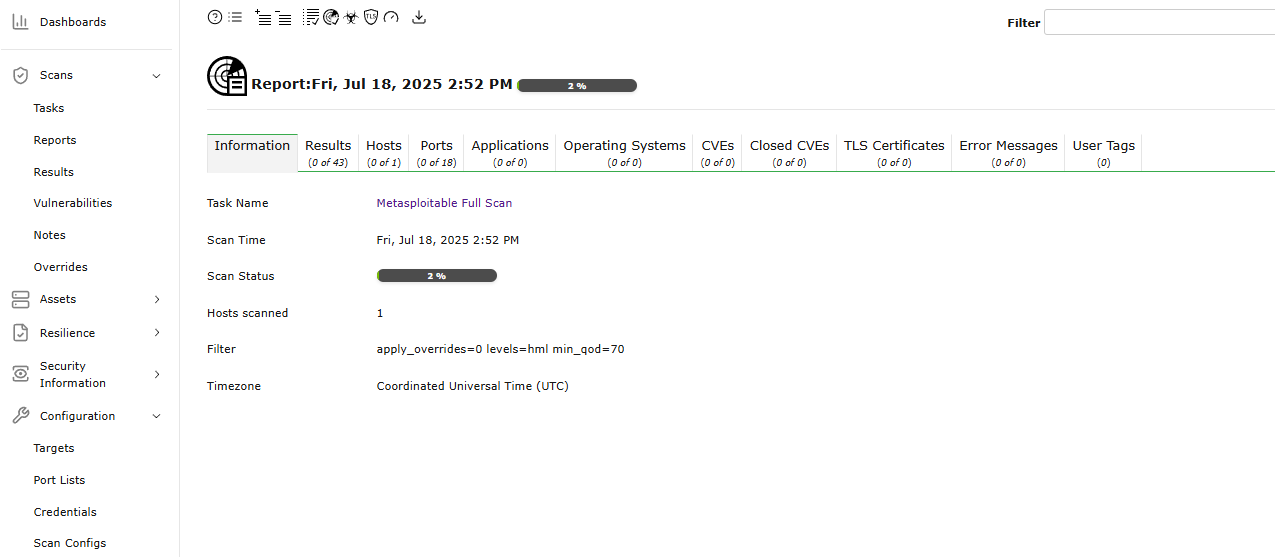
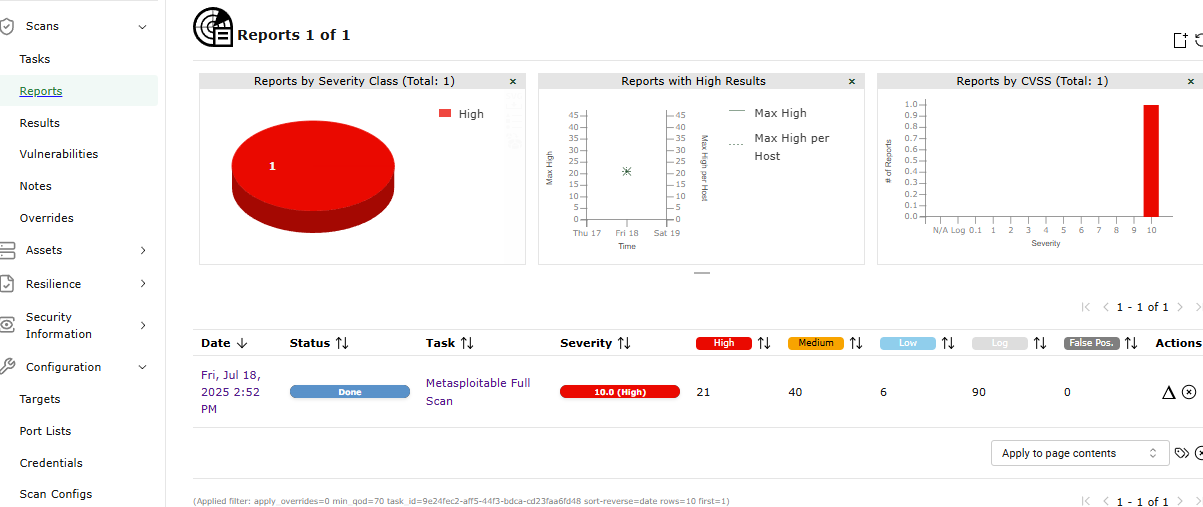
I performed a comprehensive vulnerability scan against the Metasploitable 2 server, which identified hundreds of findings. I then triaged these results based on severity, using the Common Vulnerability Scoring System (CVSS) score.
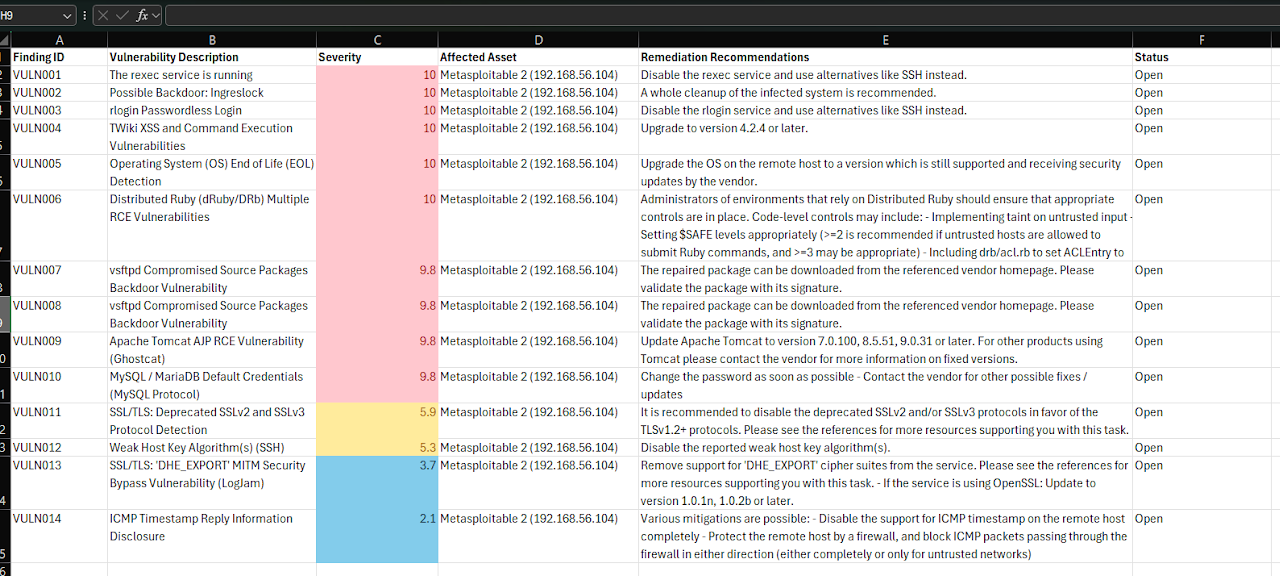
Focusing on the most critical and high-risk vulnerabilities, I translated them from the technical scanner output into a formal Plan of Action & Milestones (POA&M) spreadsheet. This involved documenting each finding, its severity, the affected asset, and the scanner's recommended remediation steps. To enhance readability and immediately draw attention to the most severe risks, I used conditional formatting to automatically color-code the severity scores (Red for High/Critical, Yellow for Medium, etc.).
What I Found
This project shows that finding vulnerabilities is only the first step; the real challenge lies in managing them at scale. A raw scan report can be operationally overwhelming, but a well-structured POA&M transforms that data into a manageable, prioritized list. It demonstrated the core function of a GRC analyst: to provide the context and structure necessary to turn technical findings into a clear and defensible business risk management plan.
Project Gallery & Step-by-Step Process
Click any image to view a full-screen slideshow with detailed explanations:
Technologies & Skills
Want to see the code or discuss the architecture?
Get in Touch